ISO 27001 – Information security, cybersecurity and privacy protection Management
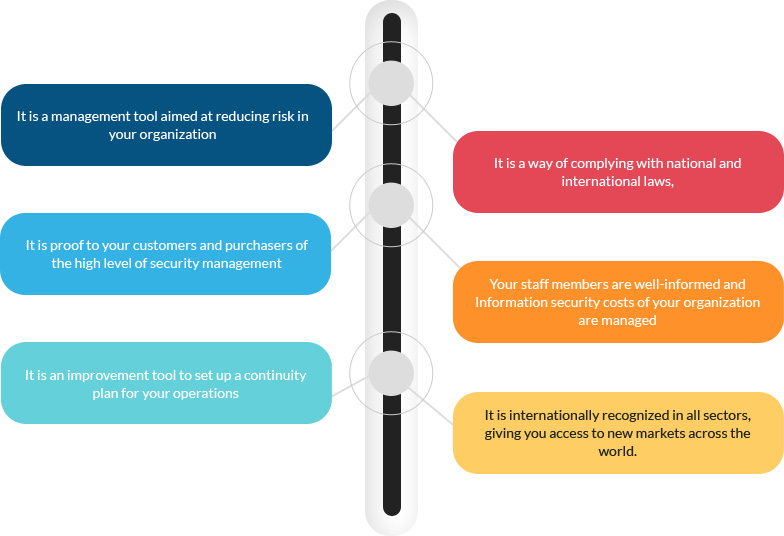
Information, for an organization, is a highly valuable asset and a powerful resource that needs to be managed and secured appropriately to operate with confidence. Increasing threats mean that ensuring you to understand what is required to control and maintain your information is now a key challenge facing most organisations. Data robbery, hacking, industrial spying, leakage, phishing, malicious code and many other threats can affect the security of your information. In today’s business environment, information security is no longer a fad, rather it is a necessity and a business enabler. The most serious impact on a business due to security breach could be loss of productivity, revenue, employee morale and customer confidence. In reference to the new EU Data Protection Ordinance, Data protection is a reactive approach towards data protection infringements which represents a high risk in view of turnover-dependent sanctions. Without suitable protection tools such as Information security, cybersecurity and privacy protection management system (ISMS), your company will be vulnerable data threats which might lead to weakened partner trust. Therefore, an active data protection management is one which significantly protects company-owned assets. The ISO 27001 is an international standard system for the management of information security specifically intended for this purpose.
WHAT IS ISO 27001 – Information security, cybersecurity and privacy protection Management standard
Information is a business critical asset because it drives growth and forms the backbone of organization. But the security of this asset is often overlooked, which is why over 80% of security breaches stem from within the organization as a result of poor policy, procedures and staff awareness training.
The security controls in operation typically address certain aspects of IT or data security, specifically, leaving non-IT information assets (such as paperwork and proprietary knowledge) less well protected on the whole.An Information security, cybersecurity and privacy protection management system (ISMS) is a management system based on a systematic business risk approach, to establish, implement, operate, monitor, review, maintain, and improve information security of an organization.The ISO 27001 Information security, cybersecurity and privacy protection management system ISMS is an International standard which focuses on maintaining critical assets those have value to the business such as;
Confidentiality:
“An unauthorized disclosure of information”. This property expresses the need that information is not made available or disclosed to irrelevant persons.
Integrity:
“Modification or destruction of data”. This property means that data cannot be altered or destroyed in an unauthorized manner, i.e. data or information should be correct and appropriate.
Availability:
“Protect against denial of service (DoS)“. This property means that an asset is accessible and useable upon demand by an authorized authority.
The standard focuses upon avoiding / reducing / mitigating risk on such assets after accessing the threats and vulnerabilitieswhich is composed of the people, processes and technological components of the organization.It outlines the process as how to put in place, an independently assessed and certified Information security, cybersecurity and privacy protection management system which allows you to more effectively secure all financial and confidential data, minimizing the likelihood of it being accessed illegally or without permission.